


What Is GDPR Compliance Services?
In the rapidly evolving digital landscape, securing individuals’ data from cyber threats has become a top priority.
The General Data Protection Regulation (GDPR) is widely regarded as the world’s strongest data protection framework. It prioritizes the data privacy of individuals within the European Union (EU) and the European Economic Area (EEA). For organizations worldwide—including those in the UAE—the GDPR provides a critical benchmark for keeping personal data collected from individuals in these regions secure and protected from breaches. The regulation took effect on May 25, 2018, replacing the EU Data Protection Directive of 1995.
GDPR compliance is not only a legal obligation but also a cornerstone of ethical business practices. For businesses, aligning with the GDPR offers a clear pathway to navigating the complexities of data protection with greater confidence and ease.
Why do organizations need it?
Achieving GDPR compliance across verticals safeguards personal data through responsible collection and secure storage, while demonstrating organizational commitment.
The GDPR obligates both data controllers (who determine processing purposes) and processors (third parties like cloud providers who process data on a controller’s behalf). Personal data now includes online identifiers (IP addresses, cookies) and biometric data (e.g., fingerprints).
For Indian companies handling EU residents’ personal data, integrating GDPR requirements is essential. Non-compliance can incur fines of up to 4% of annual global turnover, and data subjects may claim compensation.


GDPR cyber security requirements
To achieve GDPR compliance, organizations must operationalize the security mandates within several critical articles.
Implement technical safeguards (e.g., encryption, access controls) and organizational policies (e.g., data handling, staff training) to protect data integrity and confidentiality by default.
Develop and maintain an incident response plan capable of detecting, assessing, and reporting qualifying data breaches to authorities within 72 hours of discovery.
Continuously evaluate the effectiveness of security controls (Art. 32) and conduct formal DPIAs for new or changed high-risk processing activities to assess and reduce risks before they occur (Art. 35).
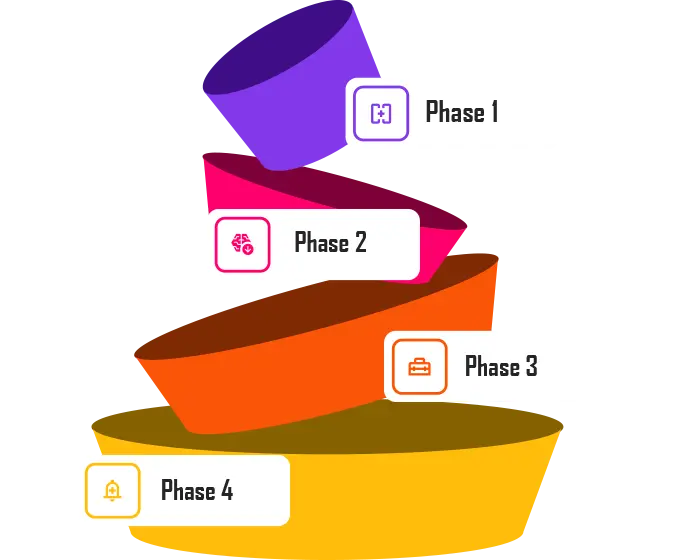
Methodology
Our Approach
We establish the compliance foundation by assessing readiness, documenting data, and training staff
We perform formal risk assessments via DPIAs to identify, evaluate, and mitigate data protection risks.
We implement practical safeguards and procedures by mapping data flows and embedding necessary controls
We ensure sustainable compliance through regular internal audits, gap analysis, and ongoing governance.
GDPR Compliance Audit & Assessment Services
Navigating the compliance and regulatory landscape—including GDPR requirements—can often be challenging. However, legal mandates and severe penalties for non-compliance make adherence to GDPR standards essential.
At Macksofy, our expert and profoundly humane team guides you through every stage of your compliance journey, ensuring security coverage against both existing and emerging threats. We never offer one-size-fits-all solutions. Instead, we provide a tailored approach that aligns perfectly with your business’s unique needs and existing practices.
Why Choose Us?
Choose Kratikal, a top-10 cybersecurity firm in India trusted by 650+ businesses. We deliver tailored compliance solutions and robust threat protection to secure your data, privacy, and future. Partner with us for confidence in a complex digital world.

We build custom GDPR roadmaps, grounded in deep experience.

We discover and classify all your personal data with tech-driven process.

High-value solutions with competitive pricing and flexible models.

Your dedicated advisor for long-term compliance and security success.